One of the most familiar healthcare regulations is the Health Insurance Portability and Accountability Act (HIPAA) of 1996, which was enacted on August 21, 1996. Even though a lot of individuals are familiar with HIPAA, it is also frequently misinterpreted. HIPAA was enacted to improve the efficiency and effectiveness of the healthcare system. The HIPAA federal regulation consists of 5 titles defined as follows:
Title I: Health Insurance Reform, which focuses on the portability of health insurance coverage between employers and prevents individuals from losing insurance due to job changes.
Title II: Administrative Simplification, which addresses the key rules regarding patient privacy and data security, including the Privacy Rule and Security Rule.
Title III: Tax-Related Health Provisions, which covers tax implications related to health insurance and medical expenses.
Title IV: Application and Enforcement of Group Health Plan Requirements, which defines the standards and enforcement mechanisms for group health plans.
Title V: Revenue Offset concerns funding mechanisms to offset the costs of implementing HIPAA regulations.
Although all 5 of the titles are related to healthcare, Title II is considered to be the most important for healthcare work force staff since it focuses on data privacy and security through the Privacy and Security Rules. Covered entities and business associates must comply with the HIPAA rules. A covered entity (CE) is a health plan, a healthcare clearinghouse, or a healthcare provider who transmits any health information in electronic form in connection with transactions covered by the HIPAA Privacy Rule. A business associate (BA) is an individual or entity who performs certain functions or activities on behalf of a covered entity that involves the use or disclosure of protected health information.
HIPAA gives patients many rights with respect to their health information. This suite of regulations includes the Privacy Rule, which protects the privacy of individually identifiable health information; the Security Rule, which sets national standards for the security of electronic Protected Health Information (ePHI); and the Breach Notification Rule, which requires covered entities and business associates to provide notification following a breach of unsecured Protected Health Information (PHI). Whether patient health information is on a computer, in an Electronic Health Record (EHR), on paper, or in other media, healthcare work force staff is responsible for safeguarding the information by meeting the requirements of the Rules.
Privacy Rule
The Privacy Rule is designed to safeguard PHI. The Privacy Rule establishes national standards for the protection of certain health information. The Privacy Rule sets standards that address the use and disclosure of PHI by covered entities. The Privacy Rule also contains guidance to help individuals understand and control how their health information is used and shared. The Privacy Rule gives patients the right to examine and obtain copies of their medical records; request corrections to their records, and restrict access to their records. The Privacy Rule permits important uses of information while protecting the privacy of individuals who seek care. A major goal of the Privacy Rule is to assure that individuals’ health information is properly protected while allowing the flow of health information needed to provide and promote high- quality healthcare and to protect the public’s health and well-being.
As a healthcare provider, you have responsibilities to patients under the HIPAA Privacy Rule, including providing them with a Notice of Privacy Practices (NPP). In addition, you must respond to their requests for access, amendments, accounting of disclosures, restrictions on uses and disclosures of their health information, and confidential communications. The Medicare and Medicaid Electronic Health Record Incentive Programs (also known as “Meaningful Use” Programs) added new rights for patients who want their healthcare providers to transmit their ePHI to themselves or other caregivers.
Security Rule
The HIPAA Security Rule establishes a national set of minimum-security standards for protecting all ePHI that a CE and BA create, receive, maintain, or transmit. The Security Rule contains the administrative, physical, and technical safeguards that CEs and BAs must put in place to secure ePHI. The Security Rule protects a subset of information covered by the Privacy Rule. This subset is all individually identifiable health information a covered entity creates, receives, maintains, or transmits in electronic form. This information is called electronic protected health information, or ePHI. The Security Rule includes security requirements to protect patients’ ePHI confidentiality, integrity, and availability. The Security Rule does not apply to PHI transmitted orally or in writing.
Your practice is responsible for taking the steps needed to protect the confidentiality, integrity, and availability of ePHI maintained in your EHR. Having an EHR affects the types and combinations of safeguards the practice will need to implement to keep their patients’ health information confidential. To comply with HIPAA Security Rule and Meaningful Use requirements, your practice must conduct a security risk analysis annually. The risk analysis process will guide you through a systematic assessment of many aspects of your practice’s business operations to help you identify potential security vulnerabilities. Once identified, your practice must implement measures to mitigate its risks.
Cyber Security Guidance
Lately, criminals have been highly successful at penetrating seen news reports of cyber-attacks, for example, national retail chains or the information networks of the federal government. Cybersecurity refers to ways to prevent, detect, and respond to attacks against or unauthorized access against a computer system and its information. Cybersecurity involves protecting your practice’s business information and/or patient information or any form of digital asset stored in your computers or in any digital memory device.
It is important to have strong cybersecurity practices in place to protect patient information, organizational assets, your practice operations, and your personnel, and of course to comply with the HIPAA Security Rule. Cybersecurity is needed whether you have your EHR locally installed in your office or access it over the internet from a cloud service provider.
Breach Notification Rule
The HIPAA Breach Notification Rule requires HIPAA-covered entities and their business associates to provide notification following a breach of unsecured protected health information. Generally, a breach is defined as an unpermitted use or disclosure of PHI, unless there is a low probability that the PHI has been compromised based on a risk assessment. When a breach of unsecured PHI occurs, the Rules require your practice to notify affected individuals, the Secretary of HHS, and, in some cases, the media. According to the regulation, a covered entity must notify authorities of most breaches without reasonable delay and no later than 60 days after discovering the breach. Breaches that affect 500 or more patients are publicly reported on the Health and Human Services Office of Civil Rights (OCR) website. Significant breaches are investigated by the Health and Human Services OCR. Penalties may be imposed for failure to comply with the HIPAA Rules.
Violations of HIPAA
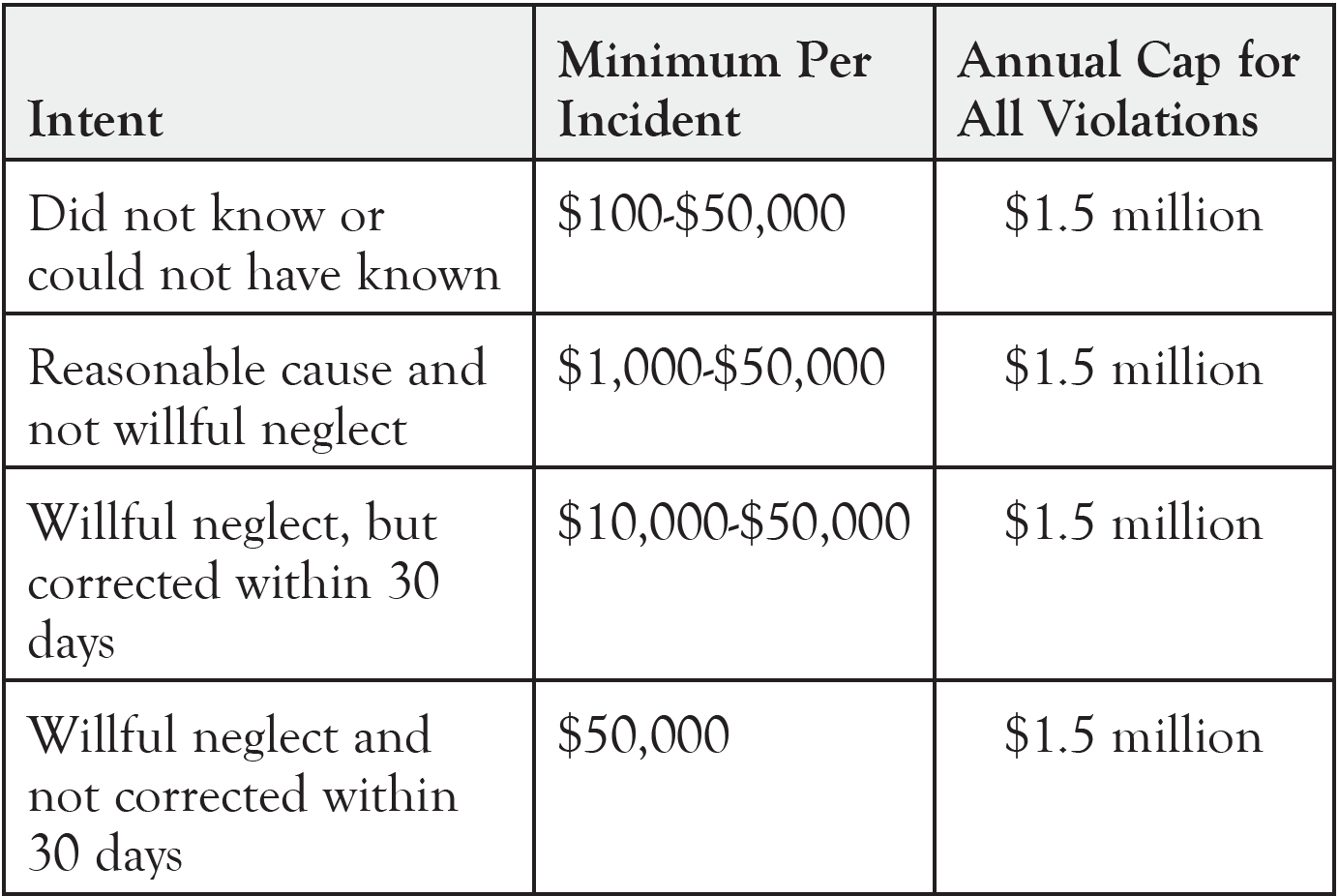
HIPAA is enforced by the Health and Human Services OCR. OCR initiates investigations upon receipt of complaints, breach reports, information provided by other agencies, and the media. Violations of HIPAA may result in civil monetary penalties. The potential civil penalties are substantial. The HIPAA Enforcement Rule provides different penalties for each of 4 levels of culpability:
- Violations that the entity did not know about and would not have known about by exercising reasonable diligence
- Violations due to “reasonable cause”
- Violations due to “willful neglect” that are corrected within 30 days
- Violations due to “willful neglect” that are not corrected within 30 days.
In some cases, the US Department of Justice may enforce criminal penalties. The US Department of Justice investigates and prosecutes criminal violations of HIPAA. Under HIPAA, the Justice Department can impose criminal penalties. An overview of the penalty amounts is as follows:
In addition to investigations that OCR conducts for potential violations of the HIPAA Rules, the OCR conducts periodic audits to ensure that CEs and BAs comply with the HIPAA Rules. Audits are not initiated because of a particular event or incident. Rather, audits are started due to the application of a set of objective criteria. HHS uses these audits as a way to examine mechanisms for compliance, identify best practices, and discover risks and vulnerabilities that may not have come to light through OCR’s ongoing complaint investigations and compliance reviews.
HIPAA Compliance
The HIPAA Rules provide a basis of federal protections for PHI. The Rules, however, are not the only laws that address the protection of health information. There are additional applicable federal, state, and local laws governing the privacy and security of health information. In some instances, a state law may be more stringent than the HIPAA Rules. For example, a state law may forbid a disclosure or require a CE or BA to get an individual’s written authorization to disclose health information, where HIPAA would otherwise permit the disclosure of the information without the individual’s permission. The individual would have to provide written authorization prior to the disclosure. The HIPAA Rules do not override such state laws that do not conflict with the Rules but offer greater privacy protections. If a state law is less protective than the HIPAA Rules but a CE or BA could comply with both, both apply—such as, when a state law permits disclosure without an authorization, and the Privacy Rule requires an authorization, the entity could comply by obtaining authorization.
It is important that your leadership team be committed to creating an organized plan and approach to integrating privacy and security into your practice’s compliance program. Activities related to maintaining patient privacy and security should be intertwined into your practice culture. Emphasis should be placed on the importance of protecting patient information and maintaining confidentiality. Reassure patients that you have a system to proactively protect the privacy and security of their health information. It is essential that the practice be able to substantiate their good-faith efforts to comply with the HIPAA Rules and regulations. A good place for the practice to start their privacy- and security-related compliance implementation is to:
- Designate a privacy & security officer
- Create privacy & security policies and procedures
- Stay abreast of privacy & security updates
- Conduct risk assessments
- Create a risk management action plan or other documentation that shows appropriate safeguards are in place throughout your organization
- Educate and train work force staff
- Maintain training materials and any associated certificates of completion
- Maintain documentation on any incidents or investigations along with their outcomes
If you are interested in a deeper dive into this topic, I invite you to join me on Thursday, May 1, from 11 am to 2 pm CST for a comprehensive HIPAA Privacy and Security Guidance for the Medical Practice 3-hour webinar. Enrollment includes a review of HIPAA policies, notices of privacy practice, restrictions of the use of PHI, and required employee training on current requirements. Participants will learn to comply with privacy and security requirements to reduce risks associated with providing telehealth services. The privacy and security of patient health information is a top priority for patients and their families, healthcare providers, ancillary professionals, and the government. However, the frequency of HIPAA and HITECH compliance enforcement is increasing. This training will help protect your practice. I am a healthcare compliance expert with extensive experience in clinical and business operations, and I will present a full review of federal legislation and enforcement efforts related to privacy and security protections for the handling of patient health information.
Learning highlights include:
- Know when a breach must be reported to HHS, and respond with confidence if a breach of unsecured health information occurs
- Prepare for new changes proposed by OCR
- Protect against cyberattacks, ransomware, and other vulnerabilities to ensure CIA of ePHI
The course fee is $239.00, but because of your affiliation with Oncology Practice Management, you may register at this link with a 20% discount using code OPM2025 https://info.pmimd.com/hipaa-privacy-for-the-medical-practice